Evaluating Crypto Ratings and Reviews: A Framework for Due Diligence

Crypto ratings and reviews attempt to compress complex protocol mechanics, token economics, and risk factors into a digestible assessment. For practitioners, these evaluations serve as screening tools rather than verdicts. Understanding how rating methodologies work, where they succeed, and where they break down determines whether a given rating adds signal or noise to your diligence process.
This article dissects the technical underpinnings of crypto ratings, identifies structural blind spots in common methodologies, and provides a framework for integrating third party assessments into your workflow without over indexing on any single source.
Core Rating Methodologies
Most crypto rating systems cluster around three approaches: quantitative scoring models, qualitative risk assessments, and hybrid frameworks.
Quantitative models pull onchain metrics (total value locked, transaction volume, unique addresses, validator count) and apply weighted formulas. A protocol might score 80/100 based on 40% liquidity depth, 30% decentralization metrics, 20% audit history, and 10% community activity. These models excel at capturing observable data but collapse nuance into a single number. A high TVL score reveals nothing about whether that capital is sticky or mercenary, nor whether liquidity is concentrated in a few wallets.
Qualitative assessments involve analyst teams evaluating smart contract architecture, governance structures, team backgrounds, and tokenomics. The output resembles traditional credit rating reports: narrative sections on technology risk, market position, and regulatory exposure, often accompanied by a letter grade or tier classification. These reviews surface context that onchain data misses but introduce subjective judgment and lag. An analyst might flag centralization risk in a multisig setup, but the assessment becomes stale the moment the protocol migrates to a DAO structure.
Hybrid models blend both inputs. They use quantitative thresholds to filter protocols, then apply qualitative overlays to refine the rating. A protocol must meet minimum liquidity and decentralization benchmarks before entering manual review. This structure improves efficiency but inherits weaknesses from both parents: the quantitative gate can exclude innovative protocols with unconventional metrics, while the qualitative layer still depends on analyst expertise and update cadence.
Structural Blind Spots
Every rating methodology carries blind spots shaped by data availability and design assumptions.
Ratings struggle with new primitives. When liquid staking derivatives emerged, existing frameworks lacked categories for rehypothecation risk or validator set correlation. Early ratings either shoehorned these protocols into unsuitable buckets or omitted them entirely. By the time methodologies adapted, market participants had already formed opinions through other channels.
Composability creates phantom risk. A protocol might receive a strong rating in isolation, but its actual risk profile depends on how it integrates with other contracts. A lending market with pristine code and robust oracles still inherits risk if it accepts collateral from a yield aggregator with opaque vault strategies. Few rating systems model crossprotocol dependencies beyond surface level integrations.
Temporal mismatches distort relevance. A smart contract audit conducted 18 months ago provides limited information about current code if the protocol ships weekly upgrades. Similarly, a governance decentralization score becomes meaningless if token distribution shifted dramatically since measurement. Ratings rarely timestamp their inputs or flag staleness thresholds, leaving users to infer data freshness.
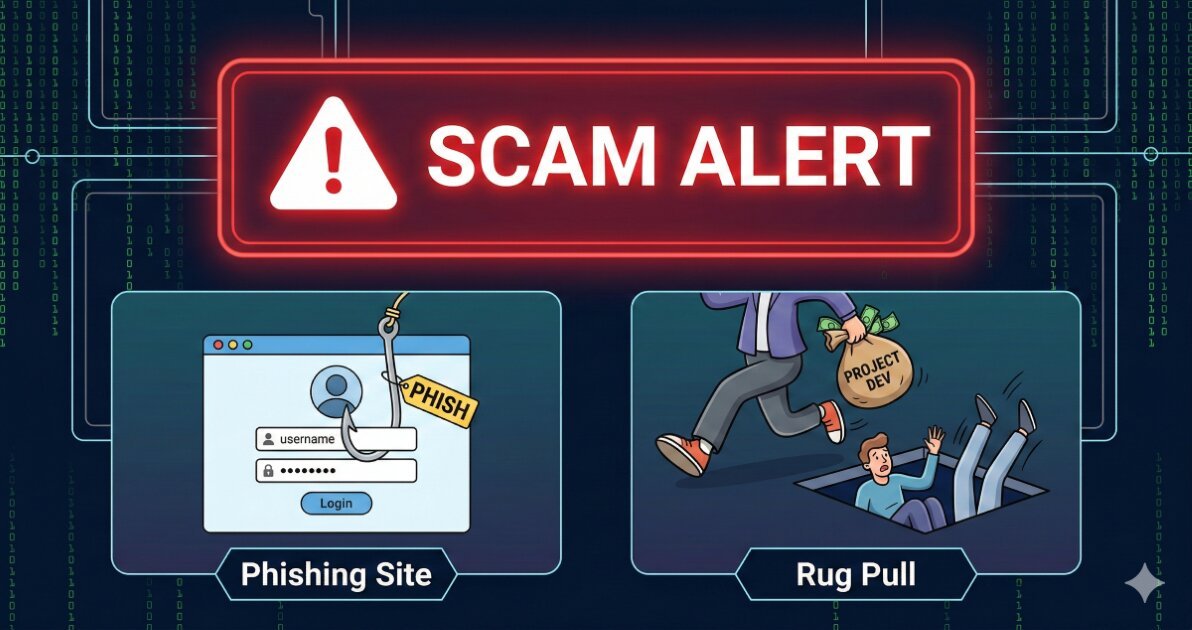
Incentive structures bias outputs. Rating agencies may accept payment from protocols for expedited reviews or enhanced listings. Others generate revenue through affiliate links or token allocations. Even absent direct conflicts, raters face pressure to avoid harsh assessments of popular protocols that drive traffic. Cross reference multiple sources and scrutinize business models before weighting any single rating heavily.
Reading Between the Lines
Extracting value from ratings requires understanding what the methodology actually measures versus what the summary score implies.
Check the input data sources. If a decentralization metric relies on publicly visible validator counts, it misses the reality that multiple validators might share infrastructure or ownership. If liquidity depth pulls from a single DEX, it ignores that most volume occurs on centralized exchanges or across multiple AMMs. Ratings that disclose data provenance let you judge whether the inputs match your threat model.
Identify the weighting logic. A protocol optimized for one rater’s formula might score poorly under another’s framework. If you care primarily about censorship resistance, a rating that assigns 50% weight to team credentials and only 10% to validator distribution provides limited insight. Reconstruct the formula when possible or focus on the subsection scores rather than the aggregate.
Look for update triggers. Some raters rescore protocols on fixed schedules (monthly, quarterly). Others update only after major events (audits, governance votes, exploits). A rating unchanged for six months might reflect methodological rigor or simple neglect. Timestamp awareness prevents anchoring on stale assessments.
Worked Example: Comparing Two Assessments
Consider a lending protocol rated by two agencies. Agency A assigns a score of 78/100 using a quantitative model: 35 points for TVL, 25 for transaction volume, 20 for audit coverage, 10 for decentralization metrics, and 10 for documentation quality. Agency B provides a qualitative tier 2 rating (on a 1 to 5 scale, where 1 is highest risk) citing strong technical execution but flagging governance centralization and oracle dependency.
Agency A’s score looks respectable. Drilling into components, you find TVL measured at a single point in time during a liquidity mining campaign. Six weeks later, TVL dropped 60% when incentives ended. Transaction volume includes both genuine borrows and wash activity from yield farmers cycling positions. The decentralization metric counts unique borrowers, not actual governance token distribution.
Agency B’s narrative reveals that three multisig signers control protocol upgrades, all affiliated with the founding team. The protocol relies on a single oracle provider with no fallback mechanism. The tier 2 rating reflects these concentrations, even though quantitative metrics appear healthy.
For your use case (assessing tail risk for a position you plan to hold through market volatility), Agency B’s qualitative breakdown surfaces critical failure modes that Agency A’s aggregate score obscures. Neither rating is wrong, but they measure different things. Your decision hinges on which dimensions matter for your specific exposure.
Common Mistakes and Misconfigurations
- Treating ratings as immutable verdicts. Protocols evolve quickly. A rating from four months ago may no longer reflect current architecture, governance, or risk profile.
- Over indexing on aggregate scores. A single number collapses multidimensional risk into false precision. Component scores or narrative sections usually hold more actionable information.
- Ignoring methodology disclosure. Agencies that hide weighting formulas or data sources prevent you from assessing whether their model aligns with your priorities.
- Assuming independence. Cross check whether the rater has financial relationships with rated protocols. Payment for ratings, token holdings, or advisory roles create conflicts that may not be prominently disclosed.
- Neglecting validator set overlap. Many rating systems treat validator count as a proxy for decentralization but fail to account for shared infrastructure, geographic concentration, or common ownership.
- Skipping crossprotocol analysis. Ratings evaluated in isolation miss risk inherited through composability, collateral relationships, or shared oracle dependencies.
What to Verify Before You Rely on This
- Rating publication date and methodology version. Confirm the assessment reflects recent protocol state, not a snapshot from multiple upgrade cycles ago.
- Data source freshness for quantitative inputs. Check whether TVL, volume, or decentralization metrics represent current conditions or point in time measurements.
- Audit scope and recency. Verify that cited audits cover the current codebase version. Protocols shipping frequent upgrades may operate on unaudited code between formal reviews.
- Business model of the rating agency. Understand whether the rater charges protocols for reviews, earns affiliate revenue, or holds tokens that create potential conflicts.
- Governance and upgrade authority. Confirm whether the protocol can be unilaterally modified, requires DAO approval, or operates under immutable contracts. Rating narratives may not reflect governance changes.
- Oracle and infrastructure dependencies. Identify single points of failure (oracle providers, bridge contracts, custody solutions) that rating methodologies might not emphasize.
- Validator or node operator concentration. For protocols where decentralization matters, verify actual ownership distribution rather than relying on raw node counts.
- Collateral and integration risk. If the protocol interacts with other contracts, assess whether the rating considers inherited risk from those dependencies.
- Legal and regulatory standing. Confirm the protocol’s compliance posture in your jurisdiction. Ratings may not cover legal risk or may reflect outdated regulatory interpretations.
- Historical incident response. Check whether the protocol has experienced exploits or governance failures since the rating was published. Post rating events matter more than the rating itself.
Next Steps
- Build a rating aggregation workflow. Pull assessments from three to five sources with differing methodologies. Focus on areas of disagreement to identify which risk dimensions matter most for your use case.
- Develop internal scoring criteria. Define the metrics and thresholds relevant to your strategy. Use third party ratings as inputs rather than outsourcing judgment entirely.
- Monitor for rating updates and protocol changes. Set alerts for new audits, governance proposals, or major liquidity shifts that invalidate existing assessments. Treat ratings as living documents, not static reference points.