Crypto Security Best Practices: Operational Framework for Self Custody and Protocol Interaction

Securing crypto assets requires treating attack surfaces as dynamically expanding. Each new wallet, protocol interaction, and contract approval increases exposure. This article covers the operational security model practitioners use to manage private keys, evaluate contract risk, and isolate failure domains. The goal is not zero risk but controlled, measurable exposure matched to asset value and recovery capability.
Key Hierarchy and Isolation Strategy
Most practitioners operate three tiers of keys, each with different security posture and access patterns.
Cold storage wallets hold long term positions and rarely sign transactions. Hardware wallets stored offline or air gapped multisig setups fit here. The key never touches an internet connected device except during carefully staged signing ceremonies. Recovery phrases live in geographically distributed secure locations, often split using Shamir Secret Sharing or multisig threshold schemes where 2 of 3 or 3 of 5 signers must coordinate to move funds.
Warm wallets handle periodic interactions with vetted protocols. These use hardware wallets that connect to networked devices only during active use. Token approvals on warm wallets get revoked immediately after swaps or LP deposits complete. Many practitioners time box these wallets, rotating addresses every 90 to 180 days and sweeping balances back to cold storage.
Hot wallets serve as transactional interfaces for frequent trading, testing, or protocol exploration. Browser extension wallets on dedicated virtual machines or separate physical devices provide moderate isolation. Maximum balance in hot wallets should not exceed what you can afford to lose in a single compromised transaction. Some operators set on chain spending limits using smart contract wallets that enforce per transaction or daily transfer caps.
Contract Interaction Surface
Every token approval grants a contract the right to transfer your tokens. The approval remains valid until explicitly revoked, persists across protocol upgrades if the contract address stays constant, and survives even if you drain your wallet to zero and refill it later.
Check active approvals monthly using tools that query the blockchain for outstanding allowance calls tied to your address. Revoke approvals for any protocol you have not used in 60 days or longer. Pay special attention to infinite approvals, where approve(spender, type(uint256).max) was called. These are standard for smooth UX but represent maximum exposure.
Before interacting with any new protocol, simulate the transaction in a fork environment or use transaction preview tools that decode the call data and show asset movements. Verify that the contract is not calling transferFrom on tokens you did not intend to move. Watch for batch transaction patterns where an innocuous swap is bundled with a hidden approval or transfer to an unrelated address.
Upgradeable proxy contracts add another layer. The implementation contract behind the proxy can change if the admin key executes an upgrade. Check whether the protocol uses a transparent proxy, UUPS proxy, or beacon proxy, and identify who controls upgrade authority. Multisig admin contracts with known signers and timelocks provide more security than single admin EOAs. Some protocols renounce upgrade capability entirely by burning the admin key, which removes upgrade risk but also prevents patching vulnerabilities.
Transaction Signing and Verification Flow
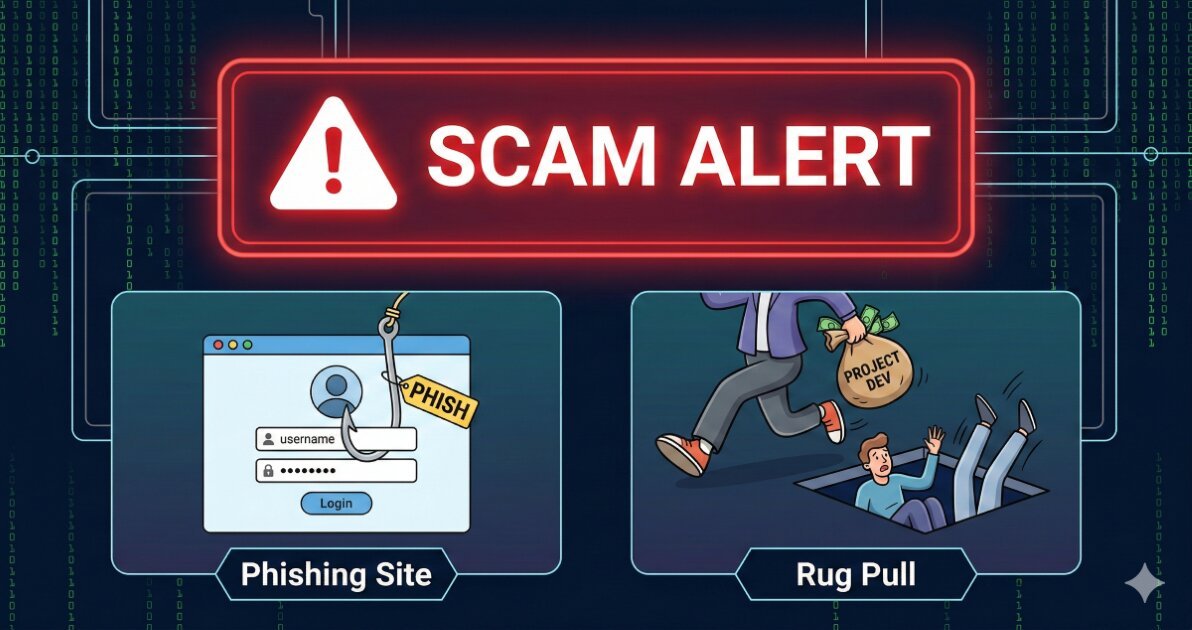
Phishing attacks increasingly target the signing moment, presenting legitimate looking interfaces that encode malicious transactions. The wallet shows only truncated addresses and hashed call data, making manual verification difficult.
Compare the contract address shown in the wallet prompt against the canonical address published on the protocol’s official site or verified block explorer page. Bookmark the protocol’s domain directly after checking DNS records and TLS certificate validity. Do not click links in Discord, Telegram, or email, even from verified accounts.
For high value transactions, decode the transaction before signing using offline tools or a separate device. Extract the call data from the wallet interface, paste it into a contract ABI decoder, and verify that function selectors, parameter values, and target addresses match your intent. This catches frontend compromises where a malicious script substitutes addresses in the final transaction.
Hardware wallets with screens provide partial mitigation by displaying transaction details independent of the host device. But screen real estate limits what you can verify. Large transfers or complex contract interactions should be staged as test transactions first with minimal amounts, then executed in full only after confirming behavior.
Multisig and Social Recovery Mechanisms
Single key custody creates single points of failure. Multisig wallets require M of N signatures to execute transactions, distributing control across multiple parties or devices.
Gnosis Safe and similar frameworks let you configure thresholds and signer sets. A 2 of 3 setup with one hardware wallet, one mobile device, and one trusted party balances security and availability. If you lose one key, the remaining two can still move funds. If one signer is compromised, they cannot act alone.
Social recovery wallets take a different approach. You designate guardians who can cooperatively reset your signing key if you lose it, typically after a timelock delay. This avoids the operational overhead of coordinating multiple signers for every transaction while still providing recovery. Guardians should be individuals or entities you trust but who do not have daily access to your funds, creating separation between operational control and recovery authority.
Both models introduce coordination and availability risks. Multisig signers must remain accessible and not lose their own keys. Social recovery guardians need secure custody of their guardian keys and must respond during recovery windows. Document the recovery process explicitly, including contact methods and fallback plans if a guardian is unavailable.
RPC and Frontend Integrity
Your wallet connects to the blockchain through an RPC endpoint. If that endpoint is compromised or malicious, it can return falsified balances, hide transactions, or present contracts with different bytecode than what exists on chain.
Run your own node when feasible, especially for high value operations. Light clients or pruned nodes reduce storage requirements while still verifying consensus. If you rely on third party RPC providers, rotate between multiple endpoints and cross check critical information like contract addresses and current nonces.
Frontend compromises happen through DNS hijacks, CDN poisoning, or malicious browser extensions. Pin the IPFS hash of the frontend for protocols that publish deterministic builds. Use hardware isolated browsers or dedicated devices for financial transactions, separate from general browsing. Extensions with broad permissions can inject scripts into any page, including your wallet interface.
Worked Example: LP Deposit with Minimal Approval Surface
You want to deposit USDC and ETH into a Uniswap V3 liquidity position. The standard flow involves approving the NonfungiblePositionManager contract to transfer your USDC, then calling mint with pool parameters.
Instead of granting infinite approval, calculate the exact amount needed for your deposit and approve only that. Query the pool’s current price to estimate token ratios, add a small buffer for price movement during transaction confirmation, and approve depositAmount * 1.02. This limits exposure if the position manager contract is later compromised or upgraded.
Simulate the transaction in a local fork to confirm the contract will only pull the approved amount and that slippage parameters are set correctly. Verify the pool address matches the canonical Uniswap factory deployment and that the fee tier is what you expect.
After the mint transaction confirms, immediately call approve(positionManager, 0) to revoke remaining allowance. The NFT representing your position sits in your wallet. Future adjustments to the position will require reapproving tokens, adding friction but reducing standing exposure.
Check the position manager’s upgrade status. At the time of Uniswap V3 deployment, the contracts were immutable with no admin keys. If interacting with a fork or similar protocol, verify this property has not changed.
Common Mistakes and Misconfigurations
Reusing seed phrases across multiple wallet implementations creates correlated failure. If one wallet’s derivation path is compromised through a software vulnerability, an attacker may try the same seed phrase in other wallets. Use unique seeds for each root identity.
Storing recovery phrases in cloud services encrypted with passwords that also live in the cloud provides only obfuscation. If an attacker accesses your cloud account through credential stuffing or session hijacking, they can retrieve both the encrypted phrase and the means to decrypt it.
Ignoring contract upgrade events means you may interact with a newly upgraded implementation without reviewing changes. Subscribe to protocol governance forums or contract event logs to track upgrade transactions, then review diff of implementation bytecode before resuming use.
Approving tokens from hot wallets that also hold large balances collapses isolation tiers. If the approval is exploited, all assets in that wallet are at risk. Transfer only the needed amount to the hot wallet before granting approvals.
Using browser wallets on the same device where you read documentation, click support links, or join community channels mixes operational and research contexts. A malicious link can exploit the wallet in the same browsing session.
Failing to test recovery procedures means you discover coordination failures or lost keys only during actual emergencies. Annually simulate multisig recoveries or social recovery flows to confirm signers are responsive and still control their keys.
What to Verify Before You Rely on This
Confirm the current contract addresses for protocols you interact with by checking official documentation or verified block explorer pages, as phishing sites replicate interfaces with substituted addresses.
Check whether contracts you granted approvals to have been upgraded recently, and review the upgrade transaction to identify changes in logic or permissions.
Verify that your RPC endpoint is returning consistent data by comparing block hashes and transaction receipts across multiple providers.
Review your active token approvals monthly and revoke any no longer needed or granted to protocols you no longer use.
Test that your hardware wallet firmware is current and that you can still access recovery phrases stored in physical locations.
Confirm multisig signer availability and that all parties can still access their signing keys, especially after long periods without transactions.
Check that browser extensions installed on devices used for wallet interactions have not added new permissions or updated in ways that expand access.
Verify that the frontend you are using matches the published IPFS hash or git commit for protocols that offer deterministic builds.
Review protocol governance proposals for any that modify admin keys, upgrade mechanisms, or fee structures that could affect your positions.
Ensure your signing device is not reusing nonces, which can happen with misconfigured hardware wallets or concurrent signing attempts, potentially exposing private keys through signature correlation attacks.
Next Steps
Audit your current wallet structure and migrate assets into a three tier hierarchy if you are currently using a single wallet for all activity, prioritizing movement of long term holdings to cold storage.
Deploy a test multisig or social recovery wallet with small amounts to familiarize yourself with the signing and recovery flows before committing significant value.
Build a monitoring dashboard or script that queries your addresses for active token approvals and alerts you to new approvals or interactions with contracts not on your whitelist.
Category: Crypto Security